目录
说明
关于kubernetes的服务暴露方式以及traefik的原理篇这里不作详细说明。traefik的原理可以参考官方文档: ,而关于kubernetes的服务暴露方式以及将traefik作为kubernetes的ingress使用的基本原理也可以参考这篇文档: 。这篇文档主要阐述将traefik作为kubernetes的ingress的实际操作,包括在traefik中启用https,将traefik的日志输出为json并通过filebeat收集,以及通过prometheus监控traefik。
部署
创建一个独立的命名空间
kubectl create ns ingress
配置rbac授权
我这里kubernetes使用1.8且启用了rbac授权。官方的traefik-rbac.yaml文件可以参考: ,但在我实际测试中,还是有问题。我这里直接采用了一个偷懒的做法,直接给了最大权限。 下面的配置文件中,先创建了一个serviceaccount名称为traefik-ingress-controller,然后直接为这个serviceaccount授予了cluster-admin的权限
traefik.rbac.yaml示例如下:
apiVersion: v1kind: ServiceAccountmetadata: labels: k8s-app: traefik-ingress-controller name: traefik-ingress-controller namespace: ingress---apiVersion: rbac.authorization.k8s.io/v1kind: ClusterRoleBindingmetadata: name: traefik-ingress-controller labels: k8s-app: traefik-ingress-controllerroleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: cluster-adminsubjects:- kind: ServiceAccount name: traefik-ingress-controller namespace: ingress
配置secret
我们将traefik作为ingress时,需要其同时处理https请求,所以需要为traefik配置证书文件。在这里将证书文件和key文件放入到secret中。我这里两个文件的名称分别是dz11.com.crt和dz11.com.key。创建secret方法如下:
kubectl create secret tls dz11-ingress-secret --key dz11.com.key --cert dz11.com.crt -n ingress
创建一个configmap用于存放traefik的配置文件
traefik.configmap.yaml配置如下:
apiVersion: v1kind: ConfigMapmetadata: name: traefik-conf namespace: ingressdata: traefik.toml: | defaultEntryPoints = ["http", "https"] [entryPoints] [entryPoints.http] address = ":80" [entryPoints.https] address = ":443" [entryPoints.https.tls] [[entryPoints.https.tls.certificates]] certFile = "/keys/dz11.com.crt" keyFile = "/keys/dz11.com.key" #traefikLogsFile = "log/traefik.log" [accessLog] filePath = "/logs/traefik.access.log" format = "json"
需要说明的是,我这里同时支持http和https,并没有做http强制跳转到https。如果需要http强制跳转到https,可以参考如下配置:
defaultEntryPoints = ["http", "https"][entryPoints] [entryPoints.http] address = ":80" [entryPoints.http.redirect] entryPoint = "https" [entryPoints.https] address = ":443" [entryPoints.https.tls] [[entryPoints.https.tls.certificates]] certFile = "/keys/dz11.com.crt" keyFile = "/keys/dz11.com.key"#traefikLogsFile = "log/traefik.log"[accessLog]filePath = "/logs/traefik.access.log"format = "json"
另外,在上面的配置中,我启动了traefik的访问日志,并将格式指定为json,这是为了方便后面直接通过filebeat作收集。这里也需要说明下,traefik的两种日志,一种是traefik服务自身的日志,另一种是访问日志。我这里只启用了访问日志。默认traefik的服务日志会通过容器的标准输出打印。
配置traefik的deployment文件
在这里我采用nodeSelecter的方式将traefik固定在指定的两个节点上,如果采用deployment的方式部署,需要在选定的节点上先打好标签。
traefik.dm.yaml配置如下:apiVersion: extensions/v1beta1kind: Deploymentmetadata: name: traefik-ingress-lb namespace: ingress labels: k8s-app: traefik-ingress-lbspec: strategy: type: RollingUpdate rollingUpdate: maxUnavailable: 1 maxSurge: 0 replicas: 2 selector: matchLabels: k8s-app: traefik-ingress-lb template: metadata: labels: k8s-app: traefik-ingress-lb annotations: prometheus.io/scrape: "true" prometheus.io/port: "8580" spec: terminationGracePeriodSeconds: 60 hostNetwork: true restartPolicy: Always volumes: - name: traefik-config configMap: name: traefik-conf - name: traefik-key secret: secretName: dz11-ingress-secret - name: traefik-log hostPath: path: /mnt/srvlogs - name: localtime hostPath: path: /etc/localtime containers: - image: dyhub.douyucdn.cn/library/traefik:v1.4.3 name: traefik-ingress-lb# resources:# limits:# cpu: 200m# memory: 30Mi# requests:# cpu: 100m# memory: 20Mi securityContext: privileged: true ports: - name: http containerPort: 80 - name: https containerPort: 443 - name: admin containerPort: 8580 volumeMounts: - mountPath: "/config" name: "traefik-config" - mountPath: "/logs" name: "traefik-log" - mountPath: "/keys" name: "traefik-key" - mountPath: "/etc/localtime" name: "localtime" args: - --configfile=/config/traefik.toml - --web - --web.address=:8580 - --kubernetes - --web.metrics.prometheus serviceAccountName: traefik-ingress-controller nodeSelector: proxy: "true" ingress: "traefik"
需要说明的是,通过volumeMounts的方式将访问日志以及https证书及密钥进行了相关挂载。然后在启动参数中,指定--web.metrics.prometheus参数以暴露metrics供prometheus收集,另外指定了管理端口为8580。
最后创建上面配置的所有资源:
kubectl create -f ./
到此,traefik在kubernetes上部署完成。
配置服务
这里是一个将traefik-ui作为traefik的代理后端的示例。
先创建一个service文件traefik-ui.svc.yaml示例如下:
apiVersion: v1kind: Servicemetadata: name: traefik-web-ui namespace: ingressspec: clusterIP: None selector: k8s-app: traefik-ingress-lb ports: - name: web port: 8580 targetPort: 8580
再创建一个traefik-ui.ingress.yaml文件如下:
apiVersion: extensions/v1beta1kind: Ingressmetadata: annotations: kubernetes.io/ingress.class: traefik name: traefik-web-ui namespace: ingressspec: tls:# - hosts:# - traefik-ui.dz11.com - secretName: dz11-ingress-secret rules: - host: traefik-ui.dz11.com http: paths: - path: / backend: serviceName: traefik-web-ui servicePort: web
创建相关资源:
kubectl create -f ./traefik-ui.svc.yamlkubectl create -f ./traefik-ui.ingress.yaml
配置好dns解析,即可通过traefik-ui.dz11.com来访问traefik-ui服务,http和https同时支持,且不会强制跳转。
通过prometheus监控traefik
在启动traefik时,使用了--web.metrics.prometheus选项,这时只需要将traefik服务的ip及admin端口添加至prometheus的配置文件中即可。如下:
- job_name: 'traefik' static_configs: - targets: ['10.1.61.147:8580','10.1.61.138:8580']
重启prometheus:
systemctl restart prometheus
在本次示例中,prometheus未运行于kubernetes中,而是独立部署
在prometheus的status的target中查看:

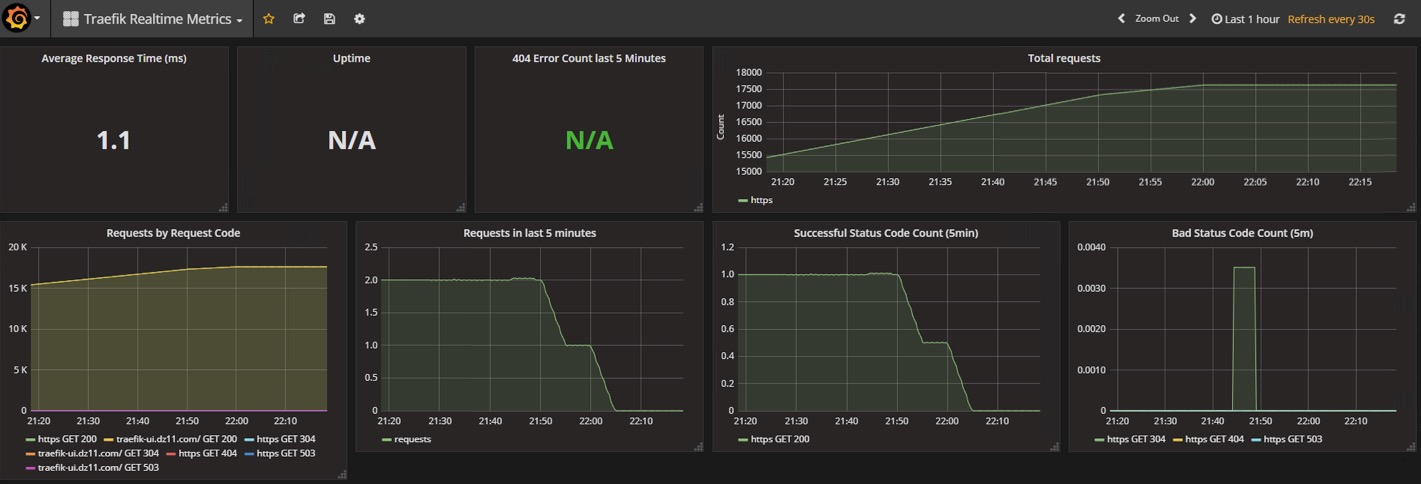
在grafana中添加dashboard,这里采用的官方的id为2870的dashboard,添加后效果如下: